NoteHomepage (by MyWay) is a browser extension that may be bundled with other free software that you download off of the Internet, or delivered via other advertising means. When installed NoteHomepage will set the homepage and search engine for your web browser to http://search.myway.com.
While installing this extension will gather information from your browsing sessions, including website visits, clicked links, and sometimes even private information, that it later sends back to display unwanted ads into your browser.
Several anti-virus scanners have marked this extension as a Browser Hijacker and are therefore not recommended to keep on your computer. It is considered potentially unwanted, and many users wish to remove it, so it is flagged for optional deletion.
About Browser Hijackers
Browser hijacking is a form of unwanted software program, usually a web browser add-on or extension, which then causes modifications in the web browser’s settings. Browser hijacker malware is developed for many different reasons. Generally, browser hijacking is utilized for earning advertising revenue from forced advert mouse clicks and site visits. Even though it might seem harmless, these tools are designed by malicious individuals who always look to take full advantage of you, so that they can earn money from your naivety and distraction. Some browser hijackers are programmed to make certain modifications beyond the browsers, like altering entries on the system registry and letting other malware further damage your machine.
Find out how to identify a browser hijack
Below are some signs and symptoms that suggest your browser has been hijacked: the home page of your browser is changed unexpectedly; your browser is constantly being redirected to adult websites; the default search engine is changed; you are getting browser toolbars you have never noticed before; never-ending pop-up advertisements show up and/or your web browser popup blocker is disabled; your web browser gets sluggish, buggy, crashes regularly; Inability to navigate to certain websites, particularly anti-malware and also other security software websites.
So how exactly does a browser hijacker infect a computer?
Browser hijackers might use drive-by downloads or file-sharing networks or an e-mail attachment in order to reach a targeted PC. They could also come from add-on programs, also called browser helper objects (BHO), web browser plug-ins, or toolbars. Browser hijackers sneak into your computer in addition to free software application downloads also that you unknowingly install alongside the original. A good example of some infamous browser hijackers includes Babylon, Anyprotect, Conduit, SweetPage, DefaultTab, Delta Search, and RocketTab, however, the names are regularly changing.
Browser hijackers will affect the user’s web surfing experience severely, track the websites frequented by users and steal personal information, cause difficulty in connecting to the web, and eventually create stability problems, causing software programs and systems to crash.
Learn how to remove browser hijackers
Some hijackers can be removed by just uninstalling the corresponding freeware or add-ons through the Add or Remove Programs in the Windows control panel. But, many browser hijackers are difficult to get rid of manually. No matter how much you try to get rid of it, it might keep returning again and again. Additionally, manual removals demand in-depth system knowledge and thus can be a very difficult job for novices.
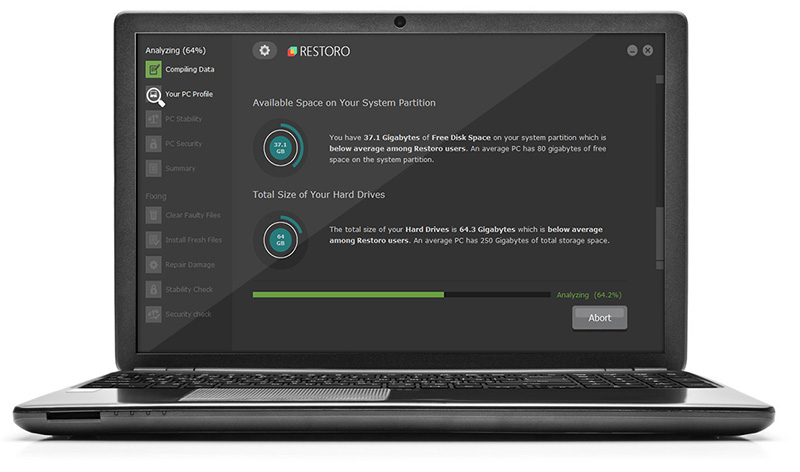
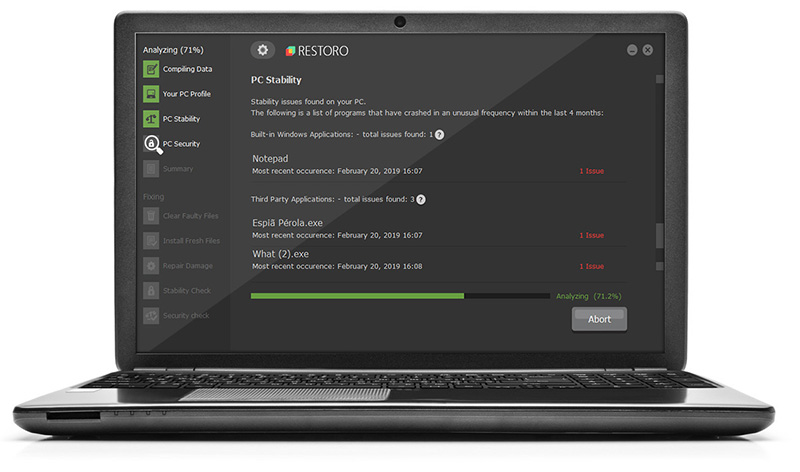
Industry experts always suggest users remove any malicious software including browser hijacker with an automatic malware removal tool, which is easier, safer, and quicker than the manual removal method. Safebytes Anti-Malware has a cutting-edge anti-malware engine to help you avoid browser hijacker infection in the first place, and mop up any pre-existing problems. Employ a pc optimizer (such as Restoro) along with your anti-malware software to solve various registry issues, remove computer vulnerabilities, and boost your computer performance.
Find Out How To Install Safebytes Anti-Malware On An Infected Computer
Malware can cause many different types of damage to computers, networks, and data. Some malware types modify internet browser settings by adding a proxy server or modify the PC’s DNS configurations. In such cases, you will be unable to visit certain or all websites, and therefore not able to download or install the required security software to clear out the malware. If you are reading this article, you may have infected by malware that prevents you from installing computer security software like Safebytes Antimalware on your PC. Although this type of problem can be difficult to get around, there are some steps you can take.
Download the software in Safe Mode with Networking
If the malware is set to run immediately when Windows starts, stepping into safe mode may block the attempt. Just minimal required applications and services are loaded whenever you start your laptop or computer in Safe Mode. To launch your Windows XP, Vista, or 7 PCs in Safe Mode with Networking, follow the instructions below.
1) At power on, hit the F8 key before the Windows splash screen begins to load. This would invoke the “Advanced Boot Options” menu.
2) Select Safe Mode with Networking with arrow keys and press ENTER.
3) As soon as this mode loads, you should have an internet connection. Now, get the malware removal software you want by utilizing the web browser. To install the program, follow the directions in the installation wizard.
4) Immediately after installation, run a full scan and let the software remove the threats it discovers.
Switch over to an alternate browser
Some viruses may target vulnerabilities of a particular web browser that obstruct the downloading process. If you’re not able to download the anti-virus software program using Internet Explorer, this means malware is targeting IE’s vulnerabilities. Here, you need to switch to a different internet browser such as Firefox or Chrome to download the Safebytes program.
Run anti-virus from a pen drive
To successfully get rid of the malware, you have to approach the problem of installing anti-malware software on the affected computer system from a different perspective. Adopt these measures to run the anti-virus on the affected computer system.
1) Download the anti-malware software on a virus-free computer.
2) Plug the USB drive into the clean computer.
3) Double click on the downloaded file to open the installation wizard.
4) Select flash drive as the location when the wizard asks you exactly where you wish to install the application. Follow the on-screen instructions to finish the installation process.
5) Remove the flash drive. Now you can utilize this portable anti-malware on the affected computer.
6) Double-click the anti-malware software EXE file on the USB drive.
7) Press the “Scan” button to run a full computer scan and remove viruses automatically.
Detect And Destroy Viruses With SafeBytes Anti-Malware
These days, anti-malware software can protect your PC from various types of online threats. But how to decide on the right one amongst plenty of malware protection software that’s available on the market? As you may be aware, there are numerous anti-malware companies and tools for you to consider. A few are really worth your money, but most aren’t. You must choose one that is efficient, practical, and has a good reputation for its malware protection. Among few good applications, SafeBytes Anti-Malware is the highly recommended program for security-conscious people.
Safebytes is one of the well-established computer solutions companies, which offer this comprehensive anti-malware program. Through its cutting-edge technology, this software protects your PC against infections brought on by different types of malware and similar internet threats, including adware, spyware, viruses, worms, trojans, keyloggers, potentially unwanted programs (PUPs), and ransomware.
SafeBytes has excellent features when compared to other anti-malware programs. These are some of the highlighted features included in the application.
World-class AntiMalware Protection: Safebytes is made on the very best virus engine within the industry. These engines will detect and remove threats even during the early stages of a malware outbreak.
Real-Time Protection: SafeBytes delivers complete and real-time security for your laptop or computer. It will check your personal computer for suspicious activity continuously and shields your personal computer from unauthorized access.
Web Filtering: SafeBytes checks the links present on a web page for possible threats and informs you if the site is safe to explore or not, through its unique safety rating system.
Fast Scan: SafeBytes’s virus scan engine is one of the fastest and most efficient within the industry. Its targeted scanning highly increases the catch rate for viruses which is embedded in various computer files.
Low Memory/CPU Usage: SafeBytes is really lightweight software. It consumes an extremely small amount of processing power as it runs in the background so you’re free to use your Windows-based computer the way you want.
24/7 Customer Service: For any technical queries or product assistance, you may get 24/7 professional assistance via chat and e-mail.
To sum it up, SafeBytes Anti-Malware is pretty great for securing your PC against all kinds of malware threats. Malware trouble will become a thing of the past when you put this application to use. If you need advanced forms of protection features & threat detections, buying SafeBytes Anti-Malware will be worth the dollars!
Technical Details and Manual Removal (Advanced Users)
To eliminate NoteHomepage manually, navigate to the Add or Remove programs list in the Windows Control Panel and select the program you want to get rid of. For web browser plug-ins, go to your web browser’s Addon/Extension manager and choose the add-on you want to disable or remove. You might also want to reset your home page and search providers, as well as clear your web browser cache and cookies.
Finally, check your hard disk for all of the following and clean your Windows registry manually to remove leftover application entries after uninstalls. Please be aware that this is for professional users only and could be challenging, with incorrect file removal resulting in additional PC errors. In addition to that, certain malware is capable of replicating or preventing deletion. You’re advised to do this procedure in Windows Safe Mode.
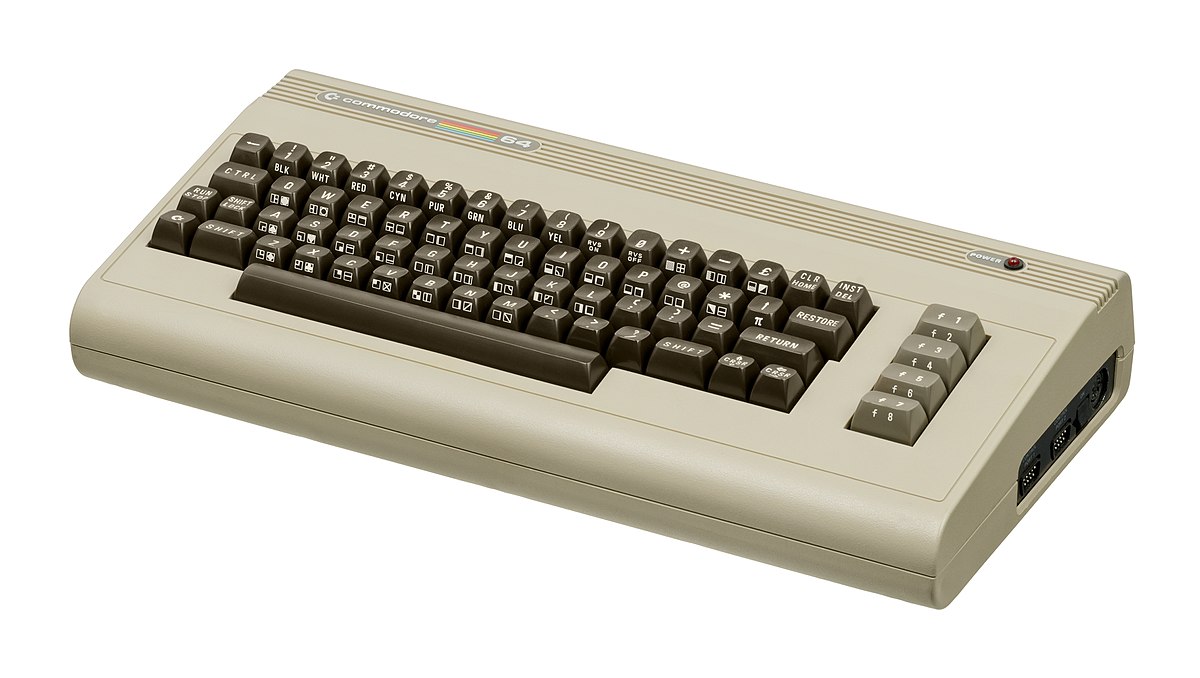 History of Commodore
History of Commodore With sales booming and the early reliability issues with the hardware addressed, software for the C64 began to grow in size and ambition during 1984. This growth shifted to the primary focus of most US game developers. The two holdouts were Sierra, who largely skipped over the C64 in favor of Apple and PC compatible machines, and Broderbund, who was heavily invested in educational software and developed primarily around the Apple II. In the North American market, the disk format had become nearly universal while cassette and cartridge-based software all but disappeared. So most US-developed games by this point grew large enough to require multi-loading.
At a mid-1984 conference of game developers and experts at Origins Game Fair, Dan Bunten, Sid Meier, and a representative of Avalon Hill said that they were developing games for the C64 first as the most promising market. By 1985, games were an estimated 60 to 70% of Commodore 64 software. Over 35% of SSI's 1986 sales were for the C64, ten points higher than for the Apple II.
Everything was great for Commodore but the industry was moving forward and by the year 1988, PC compatible computers were stated to be the largest and fastest-growing home entertainment systems pushing C64 on to second place. Also, Nintendo’s gaming system has started to take hold in the world with amazing 7 million systems sold in 1988 only.
By the year 1991, many developers exited the gaming market for Commodore 64 home computer system and its popularity started to fall due to lack of software and not so many hardware changes.
With sales booming and the early reliability issues with the hardware addressed, software for the C64 began to grow in size and ambition during 1984. This growth shifted to the primary focus of most US game developers. The two holdouts were Sierra, who largely skipped over the C64 in favor of Apple and PC compatible machines, and Broderbund, who was heavily invested in educational software and developed primarily around the Apple II. In the North American market, the disk format had become nearly universal while cassette and cartridge-based software all but disappeared. So most US-developed games by this point grew large enough to require multi-loading.
At a mid-1984 conference of game developers and experts at Origins Game Fair, Dan Bunten, Sid Meier, and a representative of Avalon Hill said that they were developing games for the C64 first as the most promising market. By 1985, games were an estimated 60 to 70% of Commodore 64 software. Over 35% of SSI's 1986 sales were for the C64, ten points higher than for the Apple II.
Everything was great for Commodore but the industry was moving forward and by the year 1988, PC compatible computers were stated to be the largest and fastest-growing home entertainment systems pushing C64 on to second place. Also, Nintendo’s gaming system has started to take hold in the world with amazing 7 million systems sold in 1988 only.
By the year 1991, many developers exited the gaming market for Commodore 64 home computer system and its popularity started to fall due to lack of software and not so many hardware changes.
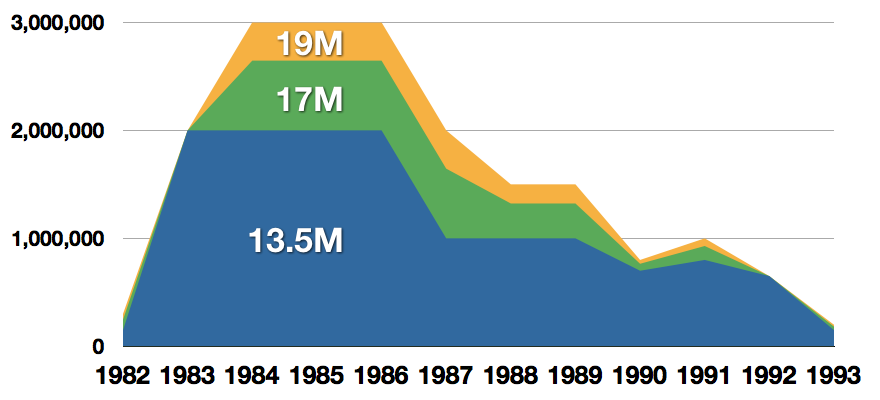 Commodore announced that the C64 would be finally discontinued in 1995.
However, only one month later in April 1994, the company filed for bankruptcy. When Commodore went bankrupt, all production on their inventory, including the C64, was discontinued, thus ending the C64's 11 and a half year production.
Commodore announced that the C64 would be finally discontinued in 1995.
However, only one month later in April 1994, the company filed for bankruptcy. When Commodore went bankrupt, all production on their inventory, including the C64, was discontinued, thus ending the C64's 11 and a half year production.
 Zak McKracken and the Alien Mindbenders
Zak McKracken and the Alien Mindbenders

 If you are not keen on spending money for reliving and checking games or software of C64 here are some links to help you to at least experience part of it completely free.
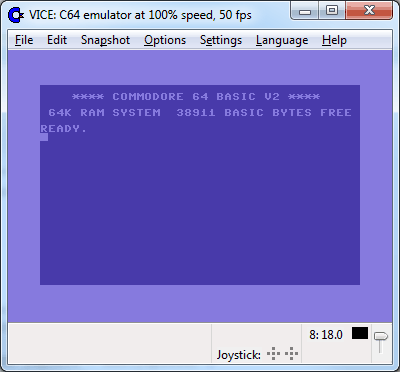
Commodore 64 Emulator
C64 Game ROMs
If you are not keen on spending money for reliving and checking games or software of C64 here are some links to help you to at least experience part of it completely free.
Commodore 64 Emulator
C64 Game ROMs


 In this article we are going to go through the best Stock Photo sites BUT, we will focus on ones that give you royalty-free Photos, so no paying stuff here, just the best of the free world.
In this article we are going to go through the best Stock Photo sites BUT, we will focus on ones that give you royalty-free Photos, so no paying stuff here, just the best of the free world.
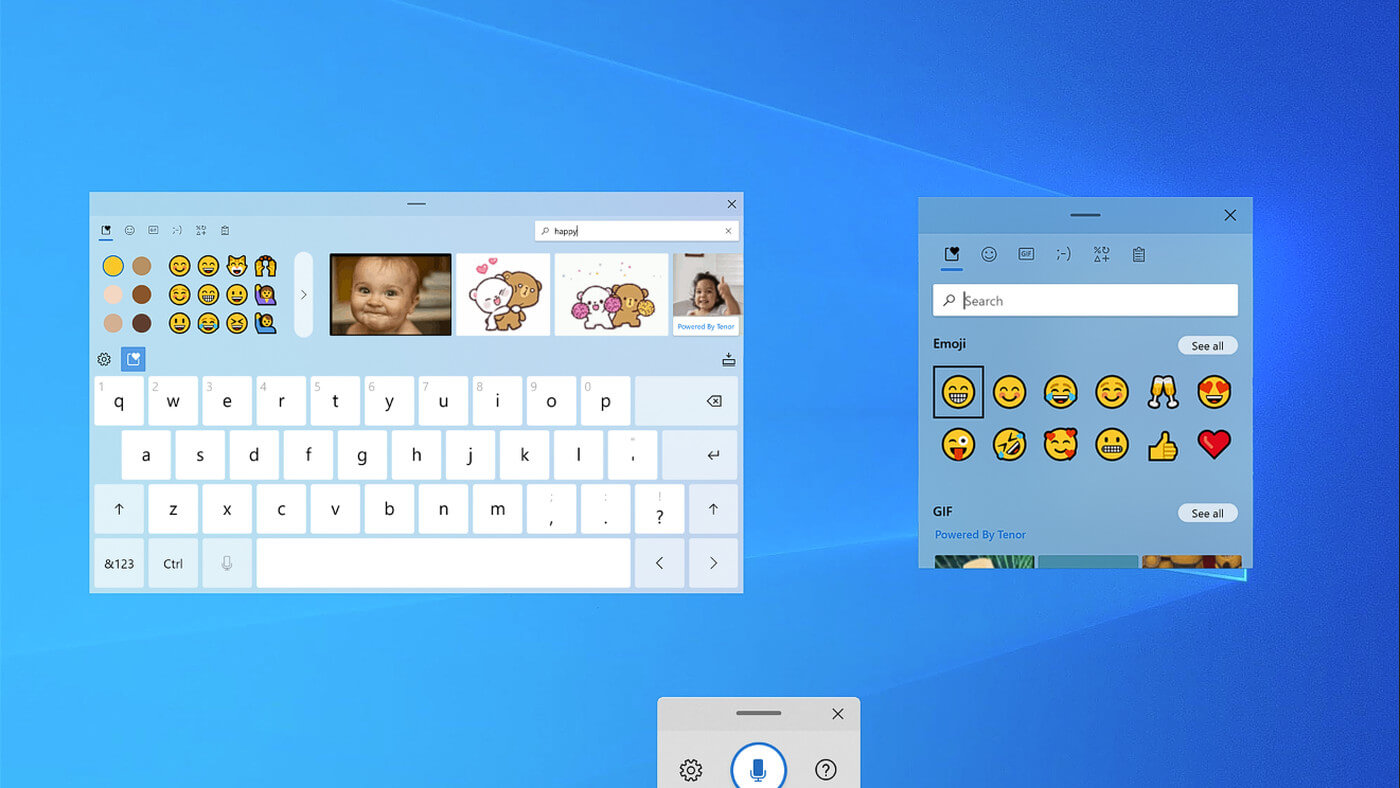 If by any chance you are working on a touchscreen PC, tablet, or any similar device and have no access to a hardware keyboard there is a way to place Touch Keyboard on your screen for easy typing, and you can enable icon on the taskbar for easy access.
If by any chance you are working on a touchscreen PC, tablet, or any similar device and have no access to a hardware keyboard there is a way to place Touch Keyboard on your screen for easy typing, and you can enable icon on the taskbar for easy access.